Leisure and Travel sector – How secure are your passwords?
- Sapphire Little

- Jan 26, 2023
- 4 min read
The Leisure and Travel sector might not seem to be the most likely target for cybercriminals but with the scattergun approach that many cybercriminals use, it is not surprising that this sector can find themselves at the mercy of this new crime type.

Hotels and airlines rely on a wide array of networks to provide reservation, payment, entertainment, and security systems. However, if a cyber-criminal gains access to a company’s system through hacking an employees or customers account, it can cause mass disruption and shut the company’s entire operation down until they receive payment to put the system back up again. For large hotels and airlines, the loss of revenue could result in being down for days. For small and medium sized companies, failure to pay the ransom could mark the end of the business altogether.
In addition, the sector has something that a lot of cybercriminals want – personable identifiable information including names, addresses and payment data. This type of information is incredibly valuable for criminals as it can be sold on for large amounts of money. Which is why having secure and unique passwords and subsequent password policies is vital.
How do hackers gain access to systems?
The quickest way for a hacker to get into a system is to log in, using the username and password of someone who already has access. According to Verzion, 80% of hacking-related breaches are linked to passwords making them a key target.
Cybercriminals use different measures for cracking passwords, for example - a trial and error of common passwords (Brute Force attack) or designing codes to crack a password by trying out various variants.
Research has shown that we are creatures of habits and when asked to create a password, there are a few things we all seem to do:
Roughly twenty-three million people still use the password:
‘123456’.
When asked to add a number to a password, most of us will add it to the end:
"Rocks1"
Over half of users have their name or date of birth in their password or use other easily discoverable information such as pet’s, partner’s or children’s name:
"Fluffy"
For work passwords we tend to use the company name somewhere:
"MyCompany1"
Finally, we tend to reuse passwords on multiple sites/systems, with employees reusing the same password an average of 13 times according to LassPass
Commonly used passwords
Criminals can create lists of these commonly used passwords and use the username/password combination to try and gain access to your systems. But they don’t just create these lists themselves, they harvest previously known passwords from other criminal’s data breaches. This is why if a password of yours ends up in a data breach, then you must assume that everyone knows it and no longer use it.
The below graphic represents the time it would take for a cybercriminal to hack (brute force) a password using current technological capabilities.
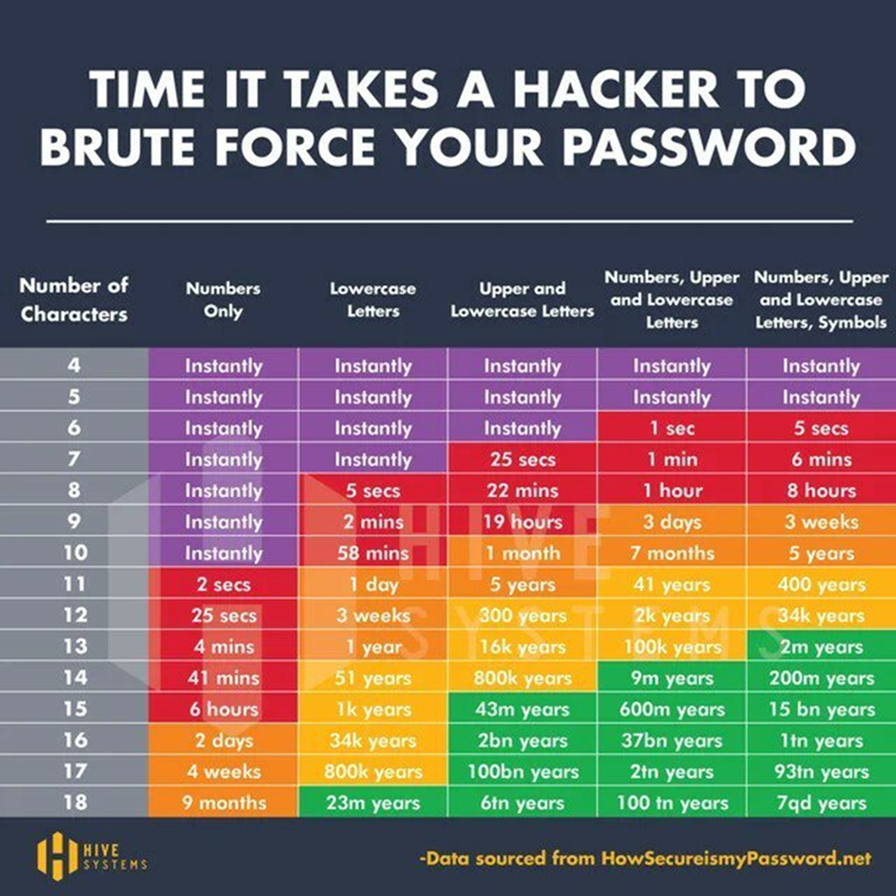
Passwords should ideally be in the green section of this table, but if one of your current passwords is in another colour - do not worry. We would just advise that change it to something more secure and unique.
The NCSC recommend use three random words followed by punctuation in order to create a secure and unique password. To find out more about passwords guidance, check out our Guidance | Eastern CRC (ecrcentre.co.uk).
Multi Factor Authentication
Two Factor Authentication (2FA) and Multi Factor Authentication (MFA) are incredibly useful in protecting your systems, accounts and devices.
2FA and MFA are essentially two or more methods that can verify your identity. A cybercriminal may be able to crack your username or password but they do not have your fingerprint, Face ID or your mobile phone to authorise a log in attempt on a mobile authenticator app.
By enabling MFA across your systems, accounts, and devices you are providing a last line of defence in a cyberattack.

What else can I do?
Here are five other things that you can do now to improve your password security:
1. See what passwords you and your staff have which have already appeared in data breaches and change them as soon as possible. Why not run a poll to see who has the most/least breaches? Haveibeenpwnded.com is a legit website where you can enter your email address and telephone number to see if your information has been captured in a data breach. You can also register your email address or domain and get notified if it appears in another breach.

2. Have a clear password policy for staff and tell them why having strong, unique passwords are essential. If you need some help with this, our affordable student services offer security awareness training. Why not make a booking to discuss further?
3. Enable 2FA and MFA wherever you can, but especially on your emails and social media accounts. Even with the best passwords, once someone knows that password then the system is no longer secure. With 2FA or MFA, even if the password and username are known, the criminal won’t have access to the second verification factor so they shouldn’t be able to just “log in”.
4. If your staff have a lot of passwords to remember, consider getting an enterprise password manager so they only have to remember one and the password manager generates and remembers the rest – saying goodbye to reused passwords.
5. Join the ECRC with free membership. Core members receive regular updates which include the latest guidance, news, and security updates as well as a series of "little steps" emails designed to get your business cyber resilient.
Further guidance & support
The Eastern Cyber Resilience Centre is a not-for-profit membership organisation, run by policing, with the intention of increasing cyber resilience of SMEs within the East of England.
You can contact the Cyber Resilience Centre for guidance and support through our e-mail enquiries@ecrcentre.co.uk or use our online booking system to make an appointment with one of our team.
We provide free guidance on our website and we would always encourage you to sign up for our free core membership. Our core membership has been tailored for businesses and charities of all sizes who are based across the seven counties in the East of England.
![CentreLogos_E [BLACK] (1).png](https://static.wixstatic.com/media/fe7eb8_06663b7d5e1f449db031e6559301c416~mv2.png/v1/fill/w_265,h_118,al_c,q_85,usm_0.66_1.00_0.01,enc_avif,quality_auto/CentreLogos_E%20%5BBLACK%5D%20(1).png)







Comments